In today’s digital time, it’s no surprise that security has become an undeniable concern. As streaming services, online tutorials, and digital marketing reach an all-time high, safeguarding the content becomes crucial to preserve intellectual property rights and ensure user privacy. Where data security is paramount, video encryption aims at ensuring your multimedia content including videos are not accessed or tampered without permission.
Explore More ✅
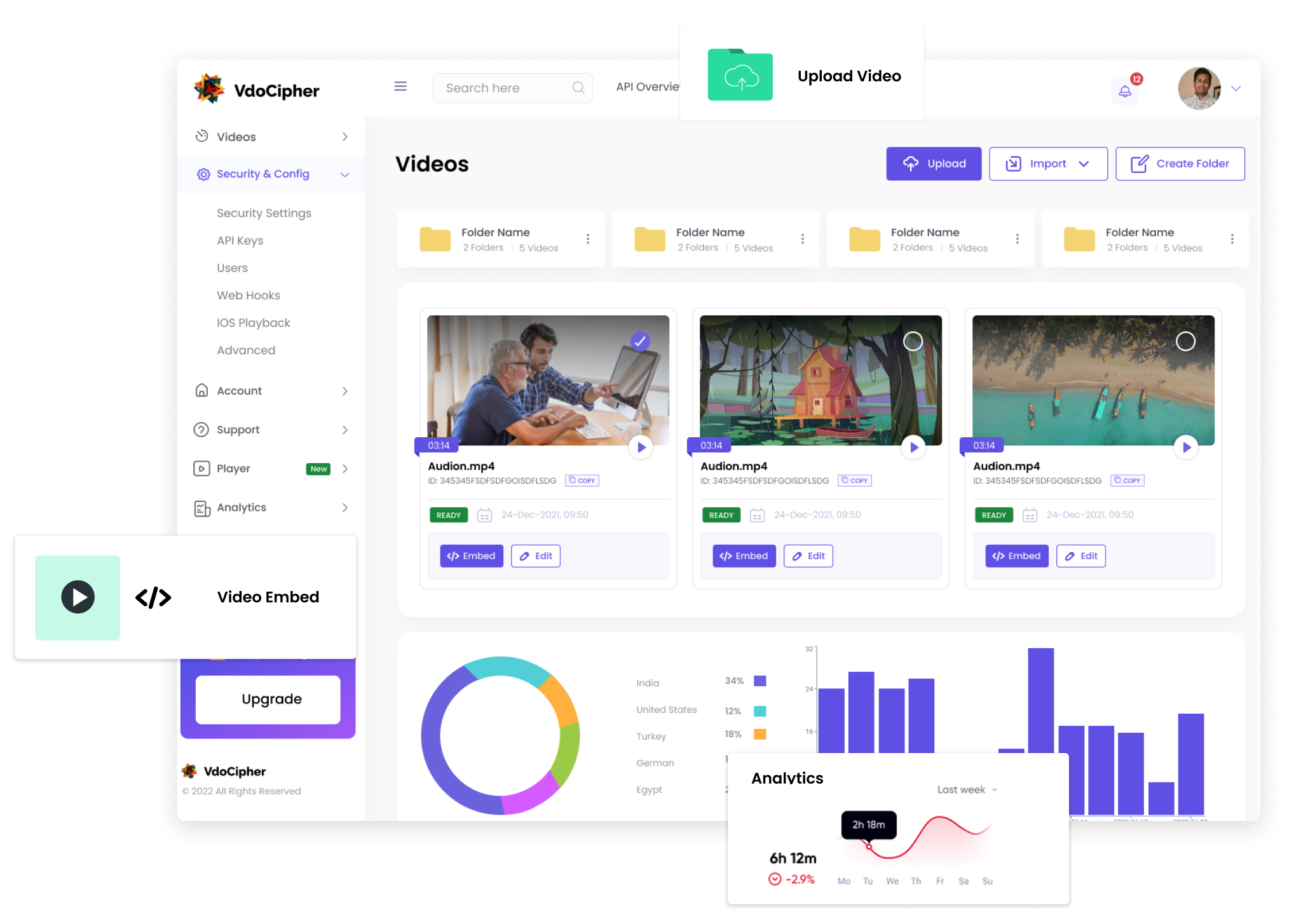
VdoCipher can help you stream your videos. You can host your videos securely, and you get various features such as Video API, CDN, Analytics, and Dashboard to manage your videos easily.
With recent statistics indicating that over 80% of all Internet traffic is video content, the importance of video encryption technology cannot be overstated. The video encryption process uses advanced algorithms to encode video data, making it unreadable to unauthorized individuals. This blog post aims to provide a comprehensive understanding of its functionality and the unique benefits it offers in a world increasingly dominated by digital video content.
What is Video Encryption & how it relates to Video Protection?
When you upload a premium course video, music video, or confidential corporate video, you surely wouldn’t want unauthorized people to access confidential company information. This is where “Video Encryption” technology comes into action for video protection.
Downloading videos via free tools & downloaders, unauthorized sharing on torrent/youtube/telegram and other platforms is a major revenue loss for any business. Once your video content is encrypted with the right protocols, you can then provide access to the ones you want to without any further risks of their downloading and sharing it at other places.
In this blog, we will provide you with an overview of various encryption technologies, relative comparison and what can you do to make it fully secure.
Video encryption is a process of digitally protecting or securing your videos to prevent unwanted interception and viewing of the transmitted videos. The process of video protection involves encrypting videos using specific software, hardware setup to secure your sensitive digital content. Anybody who tries to access or view the encrypted videos will not get access to raw videos directly; and will only get an encrypted file playing via a video player on their website or app.
One of the most important and the foremost things for any encryption system is that it should be making use of a high secure algorithm. Otherwise, there is no use in spending hundreds of dollars on a video encryption system which is again prone to download via some hack or downloader/plugin tool.
Partial encryption of streaming content and open key exchange for decryption are the main flaws that lie in these encrypted video streaming technologies and thus make them vulnerable.
Many tools are widely available over the internet that can even download encrypted videos and makes your video content easily available for everyone. We will cover more on types of encryption technologies and relative comparison below.
5 Types of Video Encryption Technologies
In protecting premium videos, encrypting a video is the easiest part. The challenge arises while making the content keys accessible to authorized video players only. The content keys are required for decrypting and play videos. If the content keys are accessible to any software/plugin/hack outside your application your videos can be easily downloaded.
Below listed are a few of the most common video encryption techniques in detail:
AES 128 Video Encryption
- Advanced Encryption Standard using a block size of 128 bits (abbreviated as AES-128), is a strong encryption standard for protecting premium content. AES-128 is the only publicly available encryption algorithm that is recommended by the NSA. Content encrypted with the Advanced Encryption Standard algorithm with 128-bit cipher block size cannot be practically decrypted by only brute force attacks.
- Flaws in AES 128 Security -Decrypting the videos on user devices without making the content keys accessible to the end-user is the bigger challenge in protecting premium videos. If a streaming service is only offering AES 128 security, chances are that someone with a good understanding of web development technologies can retrieve the key. Content Protection using just AES-128 is the programmatic equivalent of buying a state-of-the-art locker for yourself, only to leave the password key written on a slip left under the doormat. Thus, just the presence of AES-128 does not guarantee complete security.
- This blog explains in detail why AES 128 is not fully secure, and how people are overcoming this challenge by making use of DRM protocols over AES.
HLS Streaming & HLS Encryption (HLS E)
- HLS Streaming ( HTTP Live Streaming) is am open-source video playback protocol developed by Apple. Though it was initiated by Apple, HLS is now supported widely across different devices and browsers. HLS Streaming is different in its working as it provides chunked data transfer (instead of a single video stream). Adding AES 128 encryption over these video chunks enables encrypted playback called HLS Encryption or HLS E.
- A loophole in HLS E security –When using HLSe, the content is encrypted by AES 128 standard and the manifest contains a link to a key for decryption of the HLS content. However, this alone does not provide complete security. As the key is once obtained, the content can be easily decrypted and redistributed. There are existing tools and hacks available to decrypt HLS Encrypted content. Thus, HLS is not considered DRM level content protection.
- For further detailed information on HLS Streaming and Encryption, you can have a look at our blog on HLS encryption & HLS Streaming.
RTMP Streaming & RTMP Encryption (RTMP E)
- RTMP was initially primarily built for live streaming. It is used to stream audio and video between Flash Media Server and Flash Player. The chief utility of the RTMP stream is in the optimization of the audio and video data transfer between the server and player. Its major use comes in Dynamic live streaming, and because of the encryption service RTMPE. Flash support has declined over time across browsers and will be officially over in 2020. Thus, the RTMPE technology use case for desktop is going to end.
- Its peak popularity was a few years ago. There are now better protocols for recorded and live videos (e.g Dash streaming) and thus use of RTMP E is not much needed.
- The security flaw in RTMPe –RTMPe wraps the RTMP streaming in a thin encryption layer and through Encrypted RTMPE, the streaming protocol provides low-level stream encryptions for high-traffic sites. RTMPE uses the Anonymous Diffie-Hellman key exchange method. The media server and the flash player together establish a shared secret key over an insecure channel. However, the initial point of secret key sharing is not secure. The media server is unable to verify the identity of the media player, thus, leaving the player with the vulnerability of man-in-the-middle attacks at session initializations. There are tools like RTMPDUMP which can do it an easy manner.
- Detailed blog on RMTPE – RTMPe Streaming: How does Secure RTMP Streaming work and flaws in security?
How is Google Widevine DRM, Apple Fairplay DRM highest security standards for video encryption?
As explained above for various encryption technologies, AES 128, RTMP E, HLS E technologies; the key exchange mechanism is ultimately not hardcore hidden. It is thus open to software/hackers getting access to the key. Thus, there are pre-existing tools like video download helper (plugin on firefox), RTMP Dump, YTD (Command line tool), HLS Fetch which is able to decrypt and download the videos streamed via these technologies.
How does DRM encryption ensure the highest secure key exchange mechanism for video protection?
DRM (Digital Rights Management) systems are effectively an add on to AES 128, HLS Encryption technologies and are the critical factor in making the key exchange mechanism super secure. Without DRM systems, Encryption technologies are open to hacks, downloads. DRM effectively ends such loopholes in video protection. The exact DRM technology varies with the device/browser and is explained in some more detail below.
Explore More ✅
Vdocipher is used by popular LMS platforms to protect their video content using Google Widevine and Apple FairPlay DRM
There are 2 primary DRM encryptions –
1. Google Widevine DRM Video Encryption
Google has certain security control/access to the browser in case of Desktop playback (Chrome via its ownership and Firefox & Edge with partnerships), OS control in the case of the Android ecosystem. Thus, it can help to make the encryption key exchange mechanism hidden on the browser/OS level.
Thus, Google Widevine DRM combined with Dash streaming on the web and Exoplayer on Android App provides the highest security in terms of encryption.
How can one use Google Widevine DRM for video protection Desktop & Android website/apps?
VdoCipher is a direct Google partner for Widevine DRM implementation. VdoCipher provides a packaged Widevine DRM + AWS hosting + player offering for customers to use. All plans including the free trial plan include Widevine DRM pre-integrated in the account.
More on Google Widevine DRM
Widevine DRM license server details
2. Apple Fairplay DRM Video Encryption
Apple has hardware+ OS level of security control/access in case of Mac Safari (not other browsers) and IOS (browsers and app both). Similar to Google, this control can help to make the encryption key exchange mechanism hidden on the hardware/OS level. In fact, since Apple is the hardware manufacturer (unlike Google who is not generally hardware-level controller in laptops/android phones), Apple can have much stricter control. So, it can even block screen capture in IOS Safari, Mac Safari, IOS App.
Thus, Apple Fairplay DRM combined with HLS E streaming on the web and player on IOS App provides the highest security in terms of encryption and also screen capture block.
How can one use Apple Fairplay DRM for video protection in IOS and Mac Safari?
VdoCipher has a ready to use key server module set up in compliance with Apple Fairplay DRM infrastructure. Apple has a separate requirement on content owner/distributor applying to Apple directly for license and then VdoCipher can integrate that license for an account. VdoCipher guides you in the process and it is relatively simple now to do it. Technically, VdoCipher takes care of everything for the Fairplay (FPS) DRM integration.
More on Apple Fairplay DRM
More on encryption comparison for DRM and non DRM video encryption technologies
Conclusion – We hope that by now you must be familiar with the term Video Encryption, DRM video encryption, and a comparison. Based on the security level required to secure videos, you can decide on encryption technology.
Also, as our article makes it clear, DRM video encryption is generally not a DIY project for video websites and apps. VdoCipher provides robust DRM video encryption software for e-learning & media businesses. There is a free full version 30 day trial here.
FAQs
Why is video encryption important?
Video encryption is critical to protect sensitive information, intellectual property, and copyrighted material. Without encryption, unauthorized individuals might steal or alter content, leading to potential financial loss and privacy breaches.
How does video encryption work?
Video encryption uses cryptographic algorithms to convert the original video data into an unreadable format. Only those with the correct decryption key can revert the video back to its original state and view it.
How does video encryption affect video quality?
Proper encryption doesn’t degrade the quality of the video. The content looks the same post-decryption as it did before encryption. However, the process can add to the video’s loading or buffering time depending on the encryption method and key exchange mechanism.
Is encrypting video files enough to secure them?
While encryption is a primary tool for securing video files, a holistic security approach includes watermarking, DRM (Digital Rights Management), secure key exchange mechanisms, and secure video players. The mentioned features are provided by VdoCipher to more than 3000 customers in over 120 countries.
How do platforms like Netflix or Amazon Prime Video ensure their videos are encrypted and secure?
Streaming platforms like Netflix or Amazon Prime use a combination of methods, including video encryption, DRM schemes, token-based authentication, and adaptive bitrate streaming to both protect and deliver their content efficiently.
What is an Encrypted video player?
An encrypted video player is a software or application designed to play encrypted video content. Encrypted video players ensure that only authorized users view the content, protecting it from unauthorized access, copying, or sharing. Encrypted video player has the ability to decrypt and play encrypted video files. The decryption usually occurs in real-time during playback.
 Direct Partner with Google for Widevine DRM
Direct Partner with Google for Widevine DRM
 AWS Standard Technology Partner
AWS Standard Technology Partner